RADIUS
The RADIUS tab is used to define the RADIUS protocol used in the test, AAA test type, the type of messages that will be generated by the NAS node, and the information included in the messages.
Parameter Index
|
General Settings (AAA Server Nodal) |
|
|
General Settings (AAA Server Node) |
|
|
CoA and Disconnect Simulator (AAA Server Node) |
|
|
Subscription Concealed Identifier |
Subscription Concealed Identifier |
|
Authentication Settings |
|
|
Accounting Settings (AAA Server Nodal) |
|
| Apply Parameter Values From Test Data File | |
|
CoA and Disconnect Simulator (AAA Server Nodal)
|
|
|
|
|
|
NAS Port and Session ID Iteration |
|
| Prepaid Service | |
Related Measurements
Different measurements are available depending on the Protocol selected.
General Settings
| AAA Test |
Use the drop-down list to select the types of transactions that are included in the test: authentication, accounting, or both. The types of transactions affect the way RADIUS sessions are connected and disconnected... Options: Authentication With Accounting, Authentication Only, or Accounting Only Default: Authentication With Accounting
Tcl parameter: AaaTestType Related Diameter Measurements |
||||
| Starting Accounting ID |
The Acct-Session-Id attribute in the RADIUS Accounting Request messages sent to the SUT. This value is used to associate the Start, Interim Update, and Stop messages for an MN's accounting session. You can also include this attribute in access request messages. Range: Up to 64 characters Default: ACCT0000 Tcl parameter: NasAccId
|
||||
| User Name and Password |
See User Credentials |
||||
| Authentication/Accounting Messages |
Tcl Parameter: RadiusNasAuthUserNameEnabled
The Wait for Acct-Start Message is used in conjunction with IP Address Allocation (on Emulator Configuration). If an Accounting Start message is not received in the provisioned time, the reserved IP address will be released. See also Accounting Message Cycle. Range: 0 — 1,000,000 Default: 20,000 Tcl Parameter: WaitAcctStartTime Related RADIUS Measurements |
||||
| NAS Identifier |
The NAS-Identifier attribute in RADIUS requests sent to the SUT, formatted as the Fully Qualified Domain Name (FQDN) of the NAS. The name must be unique within the scope of the SUT. Either the NAS-IP-Address or the NAS-Identifier attribute is required by RADIUS. Use the checkboxes in the Authentication and Accounting panes to include the attribute in Access Request and Accounting Request messages respectively. If more than one NAS is used in the test, a unique name must be provisioned for each NAS. The default value will produce unique names in the format spcoastn@nasdomain, where n begins at 1 and increments for each NAS. Alternatively, you can use the Auto-Increment feature to generate custom names. Range: <host name>@<domain> Default: @nasdomain Tcl Parameter: NasIdentifier |
||||
| Retry Time and Retry Count | See Retries | ||||
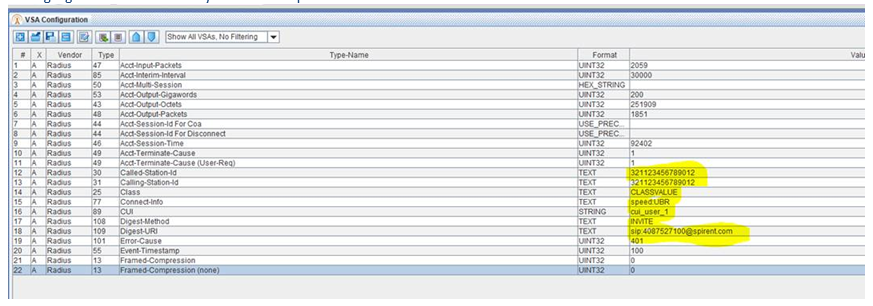
| VSA Configuration |
Use the Vendor-Specific Attribute (VSA) Configuration to define the templates used to create Radius attributes |
||||
| VSA Database Size |
Indicates the VSA size allocated for authentication packet flow descriptors and allows you to define the database memory to run VSA packets. This is the memory allocated for the overflow data caused by VSA values that take up > 4 bytes. All VSAs that have values larger than 4 bytes will be stored in the Database. In the example below: The UNIT32 is just 4 bytes 4*8=32 bits thus it will not use the database. The HEX_STRING is empty and the USE_PRECONDITION has no value. Only the Text and String Values that are highlighted below will use the database and would require about 128 bytes for the Database size. DB Size (bytes) has been added to the VSA/AVP configuration window. This is the value the AVP Database estimator calculates that is required for the AVP Database size in tabs such a Diameter, Radius, Etc. It should be used when determining the size of the AVP Database Size in Bytes.
During AAA Server Node testing, you may specify separate VSA size allocated for authentication and accounting packet flow descriptors. Range: 200 — 4,000 Default: 200 Tcl Parameters:
|
||||
| Class Attribute Size (bytes) |
Indicates the Class Attribute Size allocated for authentication/accounting Class Attributes. Range: 20 — 4,000 Default: 420 Tcl parameter: RadNasClassSize
|
||||
|
Select to View/Edit criteria based on VSAs. Define VSA Criteria, that get associated with VSA Criteria measurements which increment when Criterion is not met. To get indication (measurement count > 0) when an AVP value==300, you must setup VSA Criterion to check for AVP!=300 and then it will increment when the value does == 300. The generated measurement will remain 0 by default and will only increment if the VSA Criterion is set to Not Present and a matching VSA type is found or if the VSA Criterion is set to match a condition (operator-format-value) the VSA type is matched and the condition is not met (false). These rules are applied on a per-message basis, use the filter to see the effective rules on a per-message basis. The Vendor and Flags have no impact on the Criterion. See additional details in VSA Criteria in VSA/AVP Template Parameters: Able to:
|
|||||
|
Indicates the VSA Criteria Database size. Range: 200 — 4,000 Default: 420 Tcl parameter: RadNasAttrCritSize Tcl parameter: RadAaaAttrCritSize
|
|||||
|
Enter the Maximum Proxy State Number. This is for authentication only. Range: 0 to 10 Default: 3 Tcl parameter: ProxyStatesNum |
|||||
|
Select Transmission protocol. Available in AAA Server Nodal and AAA Server Node Test cases. If TCP is selected, the TLS tab is automatically available for input (per RFC 6614 - TLS Encryption over RADIUS). This is a licensed feature. Options: UDP (default) or TCP Tcl parameter: RadTransProtocol |
|||||
|
Available if Transmission Protocol = TCP. Enter the number of peers. Available on AAA Server Node test case. Range: 1 to 30 Default: 1 Tcl parameter: RadNumPeers |
|||||
|
Available if Transmission Protocol = TCP. Enter Watchdog time in seconds. Range: 6 to 65535 Default: 30 Tcl parameter: RadWatchDogTime |
|||||
|
Available if Transmission Protocol = TCP. Enter SUT TLS port. Range: 0 to 65535 Default: 2083 Tcl parameter: RadTlsPort |
|||||
|
Available if Transmission Protocol = TCP. The shared secret between a RADIUS TLS and AAA server that is included, along with other values, in the encrypted Authenticator field in the Access Request messages sent to the SUT. If more than one NAS node is used in the test, you can use the Auto-Increment feature to generate a unique secret for each NAS node. Select to enable TLS Secret and enter the secret.
Range: N/A Default: radsec Tcl parameter: RadTlsSecretEn Tcl parameter: RadTlsSecret |
Authentication Settings
The following parameters are available when a test includes authentication.
|
During AAA Server Nodal testing, use the radio buttons to select the type of authentication performed by the SUT. Options: CHAP, PAP, EAP, or DIGEST (DIGEST is only supported with RADIUS) When you select CHAP, you can define the Challenge Length in the field provided. Range: 1 — 128 Default: 16 When you select EAP, you can configure the methods that will be supported and the credentials used for each method with the EAP Settings window. RADIUS TestingIf the challenge length is not 16, the challenge is placed in the CHAP-Challenge attribute by default. Otherwise, the challenge is placed in the Request Authenticator field and the CHAP-Challenge attribute is not used unless you select Message Always Includes the CHAP Attribute. Related RADIUS Measurements Use the checkbox to request that the AAA SUT allocate and return an IP address for an MN in the authentication response message. When address allocation is used, the address received is automatically included in the Framed-IP-Address attribute in any accounting requests sent to the SUT.
Tcl parameter: RadiusAuthType Tcl parameter: RadiusChapChallengeLen |
||||
|
During AAA Server Node testing, Use EAP Authentication to enable EAP authentication support for a AAA server. You can configure the methods that will be supported and the acceptable credentials for each method with the EAP Settings window.
Tcl parameter: UseEapEn Selecting Use EAP Authentication enables the following:
Tcl Parameter: RadiusMusername Tcl Parameter: RadiusEapSendMsk |
||||
|
During AAA Server Node testing, select Use Digest Authentication and the relevant realm, algorithm, and QOP for Digest authentication.
|
||||
|
Enable to Increment Source port with each EAP Session. Only available when Authentication Type = EAP and Test case is AAA Nodal and Transmission Protocol is not equal to TCP. Tcl Parameter: RadNasIncSrcPortEn |
||||
|
The UDP port that is used for RADIUS authentication on all SUTs. During AAA Server Node testing, you may specify separate the AAA SUT ports for authentication and accounting. Range: N/A Default: 1812 Tcl Parameter:
|
||||
|
The shared secret between a RADIUS NAS and AAA server that is included, along with other values, in the encrypted Authenticator field in the Access Request messages sent to the SUT. If more than one NAS node is used in the test, you can use the Auto-Increment feature to generate a unique secret for each NAS node.
Range: N/A Default: secret Tcl Parameter:
Related RADIUS Measurements |
||||
|
During AAA Server Nodal Testing, when the Authentication Type is DIGEST, you can configure the RADIUS Extension for Digest Authentication settings in this sub-pane.
Options: Draft or Final Default: Final
String for the realm-value of digest-response. Default: nas.com
Method string for the request-URI of digest-response. Default: INVITE
String for the digest-uri-value of digest-response. Default: sip:[email protected]
Option for the algorithm of digest-response. Options: MD5 or MD5-sess Default: MD5
Option for the qop-value of digest-response. Options: auth or auth-int Default: auth |
||||
|
Use the checkboxes to provision the following attributes in RADIUS Access Request messages with values defined in or generated by the test case. |
||||
|
Use the checkbox to request that the AAA SUT allocate and return an IP address for HA in the authentication response message. When address allocation is used, the home address received in the MIP Registration Reply is automatically included in the Framed-IP-Address VSA in any the RADUIS Accounting Request sent to the SUT. The IP address from this parameter is also transferred to the following messages including MIP RRQ, ACCESS-REQUEST if PDF RADIUS, and Accounting-Request. Tcl Parameter: NasAaaIpAddAllocFeatEnabler
|
||||
|
If this box is checked, the CHAP Challenge value will always be included in the CHAP-Challenge attribute regardless of the challenge length. Tcl Parameter: RadiusUseChapAttributeEnabled |
||||
|
The NAS-Identifier attribute is included and is provisioned with NAS Identifier. Tcl Parameter: RadiusAuthNasIdentifierEnabled |
||||
|
Only enabled when EAP is selected. Select to not override User Name with EAP Identity. Tcl Parameter: RadiusAuthDontOverwriteUsernameEn |
||||
|
The Acct-Session-Id attribute is included and is provisioned with Accounting ID. Tcl Parameter: RadiusAuthAccountIDEnabled
|
||||
Tcl Parameter: RadiusAuthNasIpAddressEnabled
|
||||
|
Use the checkbox to enable Proxy-State attribute handling if there is a proxy AAA Server between the NAS and the authenticating server. Tcl Parameter: RadiusSendProxy
|
||||
|
Available in HA Nodal test case. When enabled, CHAP and Challenge Length (bytes) Authentication become available for input. Select to use CHAP Attribute in DMU Initial Request on AAA Tab. Tcl Parameter: DmuInitReqUseChapAttr |
||||
|
Use the check box to enable using a unique authenticator. Tcl Parameter: RadNasUniqueAuthEn
|
||||
|
Enabling the Reauthenticate Intervals checkbox and specifying the interval to re-authenticate, Enabling the checkbox causes and specifying the interval to re-authenticate, ensures that the current session is re-authenticated according to the specified interval. |
||||
|
In Wifi Offload Gateway Nodal TC, select to include the format of the Called-Station-ID with the MAC address and SSID of the WLAN the client is connecting from (used for identification/authentication purposes). Available when you select UE Authentication on the Mobile Subscriber pane. Options:
Tcl Parameter:
|
||||
|
When your RADIUS test requires that another network element participate in user authentication, such as an HA in a CDMA2000 Mobile IP test, you can add a generic NAS node that also sends Access Requests to the AAA SUT. Use the Alternate Node checkbox to enable the Alternate Node authentication, and the Alternate Node pane on the RADIUS tab is enabled, allowing you to define the NAS emulator.
Range: 1 — 100,000 Default: 1
|
Accounting Settings
During AAA Server Nodal testing, the following parameters are available when the test includes accounting.
| SUT (AAA) Port |
The UDP port that is used for RADIUS accounting on all SUTs. Range: N/A Default: 1813 Tcl Parameter: NasAccPort
|
||||||
| NAS Accounting Secret |
The shared secret between a RADIUS NAS and a AAA server that is included in the encrypted Authenticator field in the Accounting Request messages sent to the SUT. If more than one NAS node is used in the test, you can use the Auto-Increment feature to generate a unique secret for each NAS node.
Range: N/A Default: secret (Enter None to use the Authentication Secret value) Tcl Parameter: NasAccSecret
|
||||||
| Send Start Message, Send Stop Message, and Send Interim Update Message |
See Accounting Message Selection Tcl Parameters:
|
||||||
| Started Time, Stopped Time, Interim Update Time, and Start Delay Time |
The variable name:
|
||||||
| Optional Accounting Request Attributes |
Use the check boxes to provision the following RADIUS attributes in Accounting Request messages with values defined in or generated by the test case.
Tcl Parameter: RadiusAccuserNameEnabled
Tcl Parameter: RadiusAccNasIpAddressEnabled
Tcl Parameter:
Tcl Parameter: RadiusMipHoaEn
|
||||||
| Ignore Accounting Response |
Use the checkbox to allow the test to continue regardless of whether Accounting Responses are received after a Start, Interim Update, or Stop Accounting Request is sent. When the box is checked the test will record timeouts and will continue to send requests if Retries are defined but will continue when the retries are exhausted. Tcl Parameter: RadiusIgnoreAccIgnoreEn
|
||||||
| Sending Accounting On/Off |
Use the checkbox to include Accounting-On and Accounting-Off Accounting Request messages in the test. These messages direct the AAA SUT to start or stop accounting services, and are sent at the beginning and end of the test respectively. If more than one SUT is used in the test, the messages are sent to every SUT. The test will not continue until a response is received for every Accounting-On request, and if Retries are exhausted before a response is received, the test case will stop regardless of the Ignore Accounting Response setting. Tcl Parameter: RadiusAccOnOffEn
Related Measurements |
||||||
| Accounting start Delay | See Accounting Message Cycle |
Apply Parameter Values From Test Data File
Rather than using auto-incrementing values in a RADIUS test, you may provision User Name, Password, and any VSA with an imported Test Data File. Select to apply parameter values from the test Data File and then click ... to choose the file. Download a sample RADIUS file by clicking the link below.
See Test Data Files for further explanation and sample files. If a sample is not found for the specific TDF, you can obtain a sample file from your Technical Support representative. You may also use the following options to select an existing TDF or create/edit TDF-CSV files (TDF-CSV Editor).
For most TDF Parameters used for Applying Parameters, each row in the file is the overridden value for a different “Session”, aka a different UE. But some TDFs are done in other dimensions, like Bearers, eNodeBs, Subscribers (2 per UE sometimes) or even Hosts, etc. Tooltips on the TDF Parameter:

Note that the “ID” is a unique ID. Please Provide the ID when reporting issues with a TDF. For TDFs that do not apply / override Parameters, but instead are just their own configuration or data or media files you won’t see TDF ID row details.
| TIP: When including large files, please be aware of memory limitations, since the TDF Editor shares memory with the Client. |
|
NOTE: The available TDF options vary. on the L3-7 | IPSec tab > IKE with RSA Settings you may only select the Certificate TDF from TAS (these are non-CSV TDFs). In addition, where applicable, any rules for defining TDFs are included in specific Test Cases. (For example, In MME Node test case, see MME Node - Provisioning TDF.) From the DMF Window, press Shift+Alt+A to display the Save DMF as Tcl window. Click the Save to File button to save as Tcl file. See additional details on Using the Tcl API.
|
|
Select/Create a new TDF-CSV |
Allows you to create a new TDF by entering a file name that doesn’t already exist or select an existing file by entering a file name that already exists. Click to open the Select Existing or Create window.
|
||
|
Upload a New TDF to TAS |
Click to import a new TDF file from your local folder and select in the test Case (instead of having to go to TDF Admin).
|
||
|
View Edit Selected TDF in TDF-CSV Editor |
Available only when you have selected a TDF on TAS. Click to open the selected file in TDF-CSV Editor (in place, that is, within the Test Case). Edit the file and save. You may also click Save As to save the edited TDF-CSV to a different library and also rename the file, if required.
|
||
|
Open Selected TDF in Standalone TDF-CSV Editor |
Available only when you have selected a TDF on TAS. Select to retrieve the CSV file and open it in the stand alone TDF-CSV Editor. |
||
|
Generate Stub TDF-CSV |
Opens an example context specific test data parametersexample context specific test data parameters, which you may save as a .CSV file or open in the TDF-CSV Editor.
|
||
|
Launch Standalone TDF-CSV Editor |
Click to open a blank TDF-CSV Editor. The Launch Standalone TDF-CSV editor options handles very large TDFs that may use too much Client memory if opened within the Test Case/in the embedded editor. You may set the standalone TDF-CSV Editor memory high to edit large TDFs. |
Tcl Parameter: RadNasCfgFileEn
|
NOTES:
username,password,attr,attr,attr user1,pass1,attrvalue1,attrvalue2,attrvalue3 You can also provision VSAs for some MNs but not others by skipping an attribute value: username,password,attr,attr,attr user1,pass1,attrvalue1,attrvalue2,attrvalue3 user2,pass2,attrvalue1,,attrvalue3 (the second attribute is not used) user3,pass3,attrvalue1,attrvalue2, (the third attribute is not used) |
Apply Test Data File to NAS Identifier
See Test Data Files for further explanation and sample files. If a sample is not found for the specific TDF, you can obtain a sample file from your Technical Support representative. You may also use the following options to select an existing TDF or create/edit TDF-CSV files (TDF-CSV Editor).
For most TDF Parameters used for Applying Parameters, each row in the file is the overridden value for a different “Session”, aka a different UE. But some TDFs are done in other dimensions, like Bearers, eNodeBs, Subscribers (2 per UE sometimes) or even Hosts, etc. Tooltips on the TDF Parameter:

Note that the “ID” is a unique ID. Please Provide the ID when reporting issues with a TDF. For TDFs that do not apply / override Parameters, but instead are just their own configuration or data or media files you won’t see TDF ID row details.
| TIP: When including large files, please be aware of memory limitations, since the TDF Editor shares memory with the Client. |
|
NOTE: The available TDF options vary. on the L3-7 | IPSec tab > IKE with RSA Settings you may only select the Certificate TDF from TAS (these are non-CSV TDFs). In addition, where applicable, any rules for defining TDFs are included in specific Test Cases. (For example, In MME Node test case, see MME Node - Provisioning TDF.) From the DMF Window, press Shift+Alt+A to display the Save DMF as Tcl window. Click the Save to File button to save as Tcl file. See additional details on Using the Tcl API.
|
|
Select/Create a new TDF-CSV |
Allows you to create a new TDF by entering a file name that doesn’t already exist or select an existing file by entering a file name that already exists. Click to open the Select Existing or Create window.
|
||
|
Upload a New TDF to TAS |
Click to import a new TDF file from your local folder and select in the test Case (instead of having to go to TDF Admin).
|
||
|
View Edit Selected TDF in TDF-CSV Editor |
Available only when you have selected a TDF on TAS. Click to open the selected file in TDF-CSV Editor (in place, that is, within the Test Case). Edit the file and save. You may also click Save As to save the edited TDF-CSV to a different library and also rename the file, if required.
|
||
|
Open Selected TDF in Standalone TDF-CSV Editor |
Available only when you have selected a TDF on TAS. Select to retrieve the CSV file and open it in the stand alone TDF-CSV Editor. |
||
|
Generate Stub TDF-CSV |
Opens an example context specific test data parametersexample context specific test data parameters, which you may save as a .CSV file or open in the TDF-CSV Editor.
|
||
|
Launch Standalone TDF-CSV Editor |
Click to open a blank TDF-CSV Editor. The Launch Standalone TDF-CSV editor options handles very large TDFs that may use too much Client memory if opened within the Test Case/in the embedded editor. You may set the standalone TDF-CSV Editor memory high to edit large TDFs. |
|
|
During AAA Server Nodal and Node testing and SGW Nodal testing, use the checkbox to include support for RADIUS Change of Authorization requests. When the node receives an Access Request, Accounting Request Start, or Accounting Request Stop message, it will send a CoA Request to the SUT of your choice. You can choose the VSAs to include in the requests depending on the type of message received from the NAS with the Applies To checkboxes and choose whether CoA Requests will only be triggered when a message is received from a particular NAS. Tcl Parameter: RadCoaSimulationEn Related MeasurementsThe CoA report tab records the messages exchanged between the AAA node and CoA SUT along with rate and error measurements.
|
|||||
|
The secret known to both the AAA node and the CoA SUT. Range: N/A (text or hexadecimal) Default: secret Tcl Parameter: RadCoaAuthSecret |
||||||
|
Use the dropdown list to determine the timing of the CoA return messages. You can delay the messages if necessary, giving the filtering or policy server adequate time to process the authentication CoA Request prior to the start of accounting. Options:
Default: CoA ACK Tcl Parameter: RadCoARet |
||||||
|
Use the checkbox to include support for RADIUS Disconnect requests. When the node sends a Disconnect Request, the AAA session stops and tears down the AAA Session immediately. Enter the following parameters:
Tcl Parameter: RadDisconnEn |
||||||
Tcl Parameter: RadCoaAcceptWaitType
Range: 5 — 65535 Default: 10 Tcl Parameter: RadCoaAcceptDelayTime
Range: 0 — 65535 Default: 0 Tcl Parameter: RadCoaReqDelayTime
Tcl Parameter: RadCoaAuthSecret
Range: 1 - 65535 Default: 5 Tcl Parameter: RadCoaRetryCount
Range: 1 - 65536 Default: 1000 Tcl Parameter: RadCoaRetryTime
Range: 1 - 65536 Default: 0 Tcl Parameter: RadCoaDisconnectDelayTime
Default: False Tcl Parameter: RadCoaDisconnectDelayEn
Tcl Parameter: RadCoaFilterAuthEn
Tcl Parameter: RadCoaFilterAcctEn
|
||||||
|
Set Iteration Limits Use the Set Iteration Limits to control how the RADIUS client iterates over the RADIUS IDs and source ports. That is, specify the NAS Port Range, Session ID Range, and IDs per Group such that when the maximum/Stop port number in the range is reached, the Session ID iteration occurs and cycles back to the Start Port Number. Tcl Parameter: RadNasLimitPortIdFeatEn Default: False NAS Port Range The NAS Port Range allows you to configure the start and end UDP source port range. The number of source ports is used to wrap around and re-use of Port and IDs/Group pairs. Range: Start: 2000 - 65535; Stop: 65535 Default: Start: 2000; Stop: 65535 Tcl Parameter:
Session ID Range The Session ID Range is a unique identifier that matches start and stop RADIUS session IDS. Range: Start: 0 - 255; End: 255 Default: Start: 0; End: 255 Tcl Parameter:
IDs per Group Use the IDs per Group to specify the number of IDs to be used with a port before using to the next port. Range: 1 - 255 Default: 1 Tcl Parameter: RadNasGroupIdentifiers For example: IDs per Group = 3, NAS Port Range: Start - 2000 and Stop - 2001
Example when port range is 1:Example when port range is 1: If the port range of 1 (Start and Stop NAS Port is the same), the first messages sent is as follows: port/0, port/1, and port/255 then wraps to port/0 again. If the response to the first port/0 is not received before sending the second message with port/0, then the results may be invalid and/or confusing.
|
||||||
|
The Prepaid Service provides prepaid billing of services. The feature allows the AAA server to check the Mobile Subscriber's available credit to determine whether to connect the subscriber to a service and how long the connection can last. The subscriber's credit is administered by the billing server as a series of quotas representing either a duration of use (in seconds) or an allowable data volume (in bytes).
Tcl Parameter: AaaPrepaidSupportEn
Tcl Parameter: AaaPrepaidVolumeUnit
Tcl Parameter: AaaPrepaidVolumeThreshold
Tcl Parameter: AaaPrepaidQuotaTypeEn
Tcl Parameter: AaaPrepaidDurationUnit
Tcl Parameter: AaaPrepaidDurationThreshold
|
Subscription Concealed Identifier
Allows you to configure the SUPI (Subscription Permanent Identifier) - Available when TWIF is enabled on AMF Nodal Test Cnfg.
|
Select to enable DMU. Tcl Parameter: RadAaaMipEnableDMU |
|
|
The Mobile Subscriber ID. Range: N/A Default: msid12345678901 Tcl Parameter: RadAaaMipMsid |
|
|
Select to enable validation of MN Authenticator. Tcl Parameter: RadAaaMipDmuValidateMnAuth |
|
|
The authenticator that will be sent from the MN to the home AAA server. Range: 0 — 16777215 (0x0 — 0xFFFFFF) when Vendor Variant = None or Range: 0x0 — 0xFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFF) when Vendor Variant = AuthenticatorExt (Only Hex allowed) Default: 123456 when Vendor Variant = None or Default: 0x123456 when Vendor Variant = AuthenticatorExt Tcl Parameter: RadAaaMipMnAuth |
|
| Vendor Variant |
Vendor Variant is used to affect the range of MN Authenticator. If AuthenticatorExt is selected, the MN Authenticator field is extended to 16 bytes and only accept Hex number with 0x prefix. Options: None (default), AuthenticatorExt Tcl Parameter: RadAaaDmuVendorVariant |
|
The decimal value of the identifier of the Public Key Organization (PKO) that issued the public key shared by the MN and the home AAA server. See Table 1 in Verizon Wireless Dynamic Mobile IP Key Update for cdma2000(R) Networks for a list of valid PKOIDs. Range: 0 — 255 Default: 10 Tcl Parameter: RadAaaPkoId |
|
|
The serial number assigned to the public key by the PKO. Range: 0 — 255 Default: 0 Tcl Parameter: RadAaaPkoi |
|
|
The serial number assigned for the public key expansion. Range: 0 — 255 Default: 0 Tcl Parameter: RadAaaPkExp |
|
|
Use the drop-down list to select the file that will provision the local peers' private key. Options: All Certificate files installed on the test server Default: N/A Tcl Parameter: RadAaaDmuPrivateKeyFile
|
|
|
The First Entry indicates a subset of the keys contained in the private key file may be used. This parameter uses a zero-based index to specify the starting key for the set. Range: N/A Default: 0 Tcl Parameter: RadAaaDmuFirstCertEntry |
|
|
The number of private keys that will be used in the test. If there are more local peers than keys, the keys will be distributed among the peers as evenly as possible. Range: N/A Default: 1 Tcl Parameter: RadAaaDmuNumofEntries |
|
|
Use the drop-down list to specify the format used in the key and certificate files. RSA format is used for files generated by the test server's CA. Options: EVP or RSA Default: RSA Tcl Parameter: RadAaaDmuFileFormat |