PC3PC8 Flows Tab
In MME Nodal testing, the PC3 Pc8 Flows tab on the PC3/PC8/Ub Interface allows for support of supplementary services : In the Proximity-based Services (ProSe) network, PC3 is the reference point between the UE and ProSe Function. PC8 is the reference point between the UE and ProSe Key Management Function. The SUT is ProSe Fn/BSF. The purpose of the Ub (Bootstrapping interface) is to create a security association between UE and BSF.
In the Proximity-based Services (ProSe) network, PC3 is the reference point between the UE and ProSe Function. PC8 is the reference point between the UE and ProSe Key Management Function. The following diagram is from TS 33.303.

The following diagram in 3GPP TS 23.303 shows that the Prose Function is a logic function in the ProSe network used for network related action.
Bootstrapping procedure is embedded in the PSk-TLS handshaking process:
HTTPS and MIKEY Based Procedures on PC3:
After PSK-TLS connection is set up successfully, various of procedures can be performed over PC3 and PC8 interfaces. The following diagram is from TS 33.303.
HTTPS and MIKEY Based Procedures on PC3/PC8
After PSK-TLS connection is set up successfully, various of procedures can be performed over PC3 and PC8 interfaces.
- Downloading/Updating MO via ProSe Public Safety Direct Services Provisioning MO (success, no auth) Built-in Action
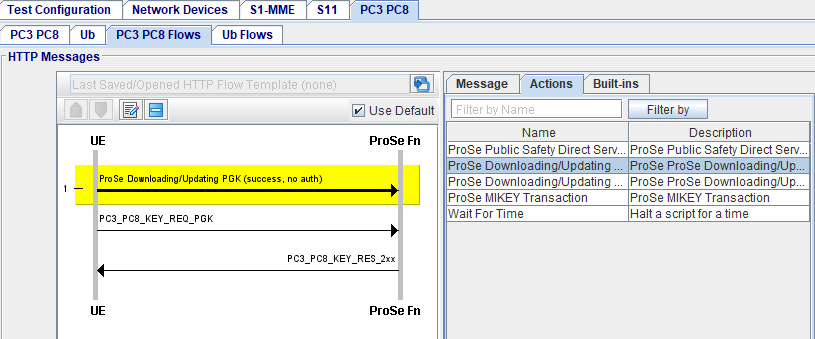
- Downloading/Updating PGK via ProSe Downloading/Updating PGK (success, no auth) Built-in Action
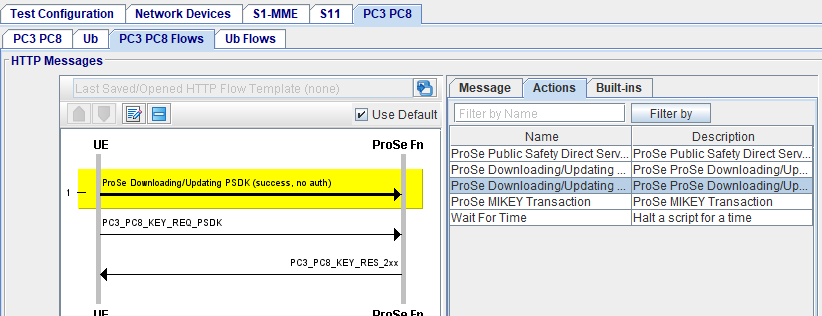
- Downloading/Updating PSDK via ProSe Downloading/Updating PSDK (success, no auth) Built-in Action
- ProSe MIKEY Transaction via ProSe MIKEY Transaction
The above procedures include some messages over HTTP, and some massages over MIKEY (which is a protocol based on udp, and may be on SIP/SDP).
This is part of the ProSe service authorization procedures over PC3 interface as specified in TS 24.334 Sub-clause 5.1, TS 24.333, and OMA-TS-DM_Protocol-V1_2.
OMA Device Management (OMA DM) protocol and SyncML protocol are used.
List of applicable documents referenced by this topic:
|
Document Number |
Title |
|
3GPP TS 23.305 Release 15 |
Proximity-based (ProSe); Stage 2 |
|
3GPP TS 24.109 Release 14 |
Bootstrapping interface (Ub) and network application function interface (Ua); Protocol details |
|
3GPP TS 24.333 Release 16 |
Proximity-based (ProSe) Management Objects (MO) |
|
3GPP TS 24.334 Release 15 |
Proximity-based (ProSe) User Equipment (UE) to ProSe function protocol aspects |
|
3GPP TS 24.623 Release 14 |
Extensible Markup Language (XML)Configuration Access Protocol (XCAP) over the Ut interface for Manipulating Supplementary Services |
|
3GPP TS 23.003 Release 14 |
Numbering, addressing and identification |
|
3GPP TS 33.804 Release 12 |
Single Sign On (SSO) application security for Common IP Multimedia Subsystem (IMS) based on Session Initiation Protocol (SIP) Digest |
|
3GPP TS 33.210 Release 14 |
Network Domain (NDS); IP network layer security |
|
3GPP TS 33.220 Release 14 |
Generic Authentication Architecture (GAA); Generic Bootstrapping Architecture (GBA) |
|
3GPP TS 33.222 Release 15 |
Generic Authentication Architecture (GAA); Access to network application functions using Hypertext Transfer Protocol over Transport Layer Security (HTTPS) |
|
3GPP TS 33.303 Release 15 |
Proximity-based (ProSe); Security aspects |
|
3GPP TS 33.310 Release 16 |
Network Domain Security (NDS); Authentication Framework (AF) |
|
Hypertext Transfer Protocol (HTTP/1.1): Message Syntax and Routing |
|
|
Hypertext Transfer Protocol (HTTP/1.1): Semantics and Content |
|
|
Hypertext Transfer Protocol (HTTP/1.1): Caching |
|
|
Hypertext Transfer Protocol (HTTP/1.1): Authentication |
|
|
HTTP Digest Access Authentication |
|
|
Pre-Shared Key Ciphersuites for Transport Layer Security (TLS) |
|
|
MIKEY; Multimedia Internet KEYing |
|
|
Hypertext Transfer Protocol (HTTP) Digest Authentication Using Authentication and Key Agreement (AKA) |
|
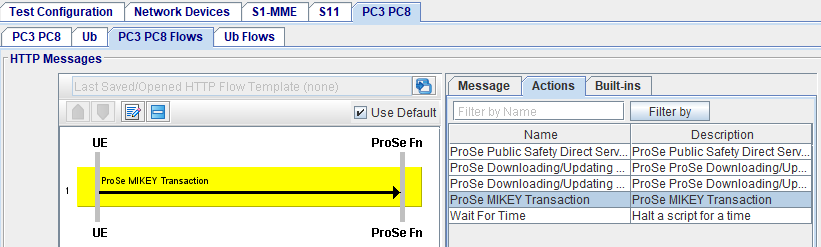
HTTP Messages HTTP Flow:
|
HTTP SCRIPT: HTTP Supplementary Script - Create HTTP tests using Scripts and Actions HTTP Message Editor (Right pane)
|
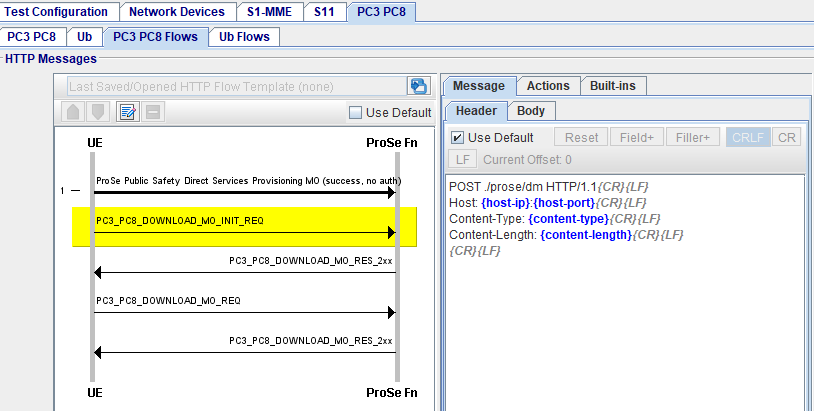
Pc3Pc8 Http Messages
The HTTP tab | HTTP Messages pane displays two columns/panes. The left pane displays HTTP message flows line diagram and the right column/pane displays the relevant message header and message body content. When you click on a message (of a flow) in the left pane, the message is highlighted and on the right column/pane, displays the HTTP message headers and Body (HTTP message body, where applicable) for the highlighted message.
A default configuration is displayed as a template and allows you to modify HTTP headers and body (XML Body), where applicable. (A template is displayed for every HTTP message available to be modified).
|
Open a HTTP Flow Template |
Click
|
|
|
Save as Data Profile Template |
Click to
|
|
|
Pop-up HTTP Flow |
Click to |
|
|
HTTP Flow Line Diagram |
Click on any HTTP Flow Message (left column) to enable HTTP Message editor (right column):
|
Pc3Pc8 HTTP Call Flow (Left Pane)
The HTTP Call Flow (Left Pane) shows a flow of messages expected for a current test configuration. When you select a message in the flow control area, default HTTP templates are shown in the editing windows (Right Pane).
The line diagram illustrates standard representation of the selected message. Each message (represented by a horizontal line) includes a text string (Field) or a combination of a text string and predefined parameter type (Filler; shown in blue on the right pane).
|
Use Default |
Selected by default. When selected, default content of HTTP headers and HTTP body are used in the test case. When not selected, the template will be used to replace the default message content. |
|
|
HTTP Flow Line Diagram |
Click on any HTTP Flow Message (left column) to enable HTTP Message editor (right column)
|
HTTP Messages Editor (Right Pane)
|
Use Default |
When selected, for all messages in the test case, Use Default is disabled for individual message (on the Right Pane). |
||||||||||
|
When not selected, individual message editor will be enabled for configuration. |
|||||||||||
|
Reset, Field+ (list), and Filler+ (list) |
Available when Use Default is not selected. The Reset, Field+ , and Filler+ buttons help you with the editing process. You may replace the original Fields and Fillers in the message Header/Body by any text.
|
||||||||||
|
|||||||||||
|
Conditional Parameters (used when parameters used in your template do not exist in the original message) |
Since a configurable HTTP message is generated from an existing message, some parameters used in your template may not exist in the original message. You may use “…-if” parameter to take care of such cases.
|
||||||||||
|
Example HTTP Header and Template |
PC3_PC8_DOWNLOAD_MO_REQ
POST . /prose/dm HTTP/1.1{CR}{LF} Host: {host-ip}{host-port}{CR}{LF} Content-Type: {content-type}{CR}{LF} Content-Type: {content-length}{CR}{LF} {CR}{LF} |
||||||||||
|
Example XML Body |
PC3_PC8_DOWNLOAD_MO_INIT_REQ: <?xml version="1.0" encoding="UTF-8"?>{CR} {LF} <SyncML xmlns="SYNCML:SYNCML1.2">{CR} {LF} <SyncHdr>{CR} {LF} <VerDTD>1.2</VerDTD>{CR} {LF} <VerProto>DM/1.2</VerProto>{CR} {LF} <SessionID>1</SessionID>{CR} {LF} <MsgID>1</MsgID>{CR} {LF} <Target>{CR} {LF} <LocURI>http://prosefn.Spirent.com:8080/prose/dm</LocURI>{CR} {LF} </Target>{CR} {LF} <Source>{CR} {LF} <LocURI>urn:oma:mo:ext-3gpp-prose-direct-provisioning:1.0:provision</LocURI>{CR} {LF} </Source>{CR} {LF} </SyncHdr>{CR} {LF} <SyncBody>{CR} {LF} <Alert>{CR} {LF} <CmdID>1</CmdID>{CR} {LF} <Data>1226</Data>{CR} {LF} <Item>{CR} {LF} <Source><LocURI>urn:oma:mo:ext-3gpp-prose-direct-provisioning:1.0:provision</LocURI></Source>{CR} {LF} </Item>{CR} {LF} </Alert>{CR} {LF} <Replace>{CR} {LF} <CmdID>2</CmdID>{CR} {LF} <Item>{CR} {LF} <Source>{CR} {LF} <LocURI>IMSI:{imsi}</LocURI>{CR} {LF} <LocName>MCPTT-ID:{public-username}</LocName>{CR} {LF} </Source>{CR} {LF} </Item>{CR} {LF} </Replace>{CR} {LF} <Final />{CR} {LF} </SyncBody>{CR} {LF} </SyncML>{CR} {LF} |
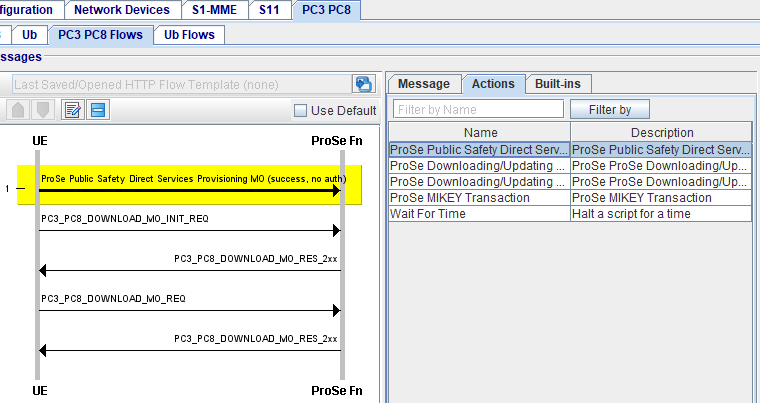
HTTP Supplementary Script
The HTTP Supplementary option provides users with a way for creating HTTP tests using scripts and actions.
The main advantage of using scripts and actions; is to allow users creating different HTTP message flows tailored to their particular test environments.
A script (a sample is shown below) consists of one of more actions.
An action performs a particular small common task in HTTP tests such as BootStrapping With BSF. Actions are fixed and predefined by Landslide software; they cannot be created by users.
|
Message |
Example UE Starts ProSe Public Safety Direct Services Provisioning MO (success, no auth) script:
|
|
PC3 PC8 Actions |
See Complete list of Actions - PC3 PC8 Actions |
|
PC3 PC8 Built-ins |
See Complete list of Built-in Scripts - Currently there are no Built-in Scripts available for PC3 PC8 Flows. |
XCAP HTTP 1.1 Methods
XCAP HTTP 1.1 Methods for Ub Client:
|
GET METHOD |
HTTP GET method can be used to fetch the xml data for a particular supplementary service. GET method can be challenged by the XCAP server. |
|
PUT METHOD |
HTTP PUT method can be used to update the xml data for a particular supplementary service. PUT method can be challenged by the XCAP server. |
|
DELETE METHOD |
HTTP DELETE method can be used to remove the xml data for a particular supplementary service or the entire document. DELETE method can be challenged by the XCAP server. |
Message flows for PC3 PC8 Supplementary services:
The following message flows will be available for each supplementary service.
User can select the supplementary service as shown in the table below.
PC3 PC8 Actions
|
ProSe Public Safety Direct Services Provisioning MO (Success, no auth) |
Downloading and Updating MO - ProSe Public Safety Direct Services Provisioning MO These procedures include some messages over HTTP, and some massages over MIKEY (which is a protocol based on udp, and may be on SIP/SDP). This is part of the ProSe service authorization procedures over PC3 interface as specified in TS 24.334 Sub-clause 5.1, TS 24.333, and OMA-TS-DM_Protocol-V1_2. OMA Device Management (OMA DM) protocol and SyncML protocol are used.
UE Sends out multiple HTTP POST messages in this procedure. The first one includes Alert command to set URI and MO ID of the ProSe safety direct provisioning MO, and a Replace command to provide IMSI and MCPTT-ID of the UE. Script a template of the message as below: Download/Update MO Initial Request
The second HTTP POST message includes Status for each of the commands in the HTTP Response message it received. Script template of the message as below: Download/Update MO Request
Fillers are available in the HTTP message templates, so each UE will be able to put dynamic information element into the HTTP POST messages. Some of the available fillers are:
|
||
|
ProSe Downloading/Updating PGK (success, no auth) |
Select ProSe Downloading/Updating PGK (success, no auth).
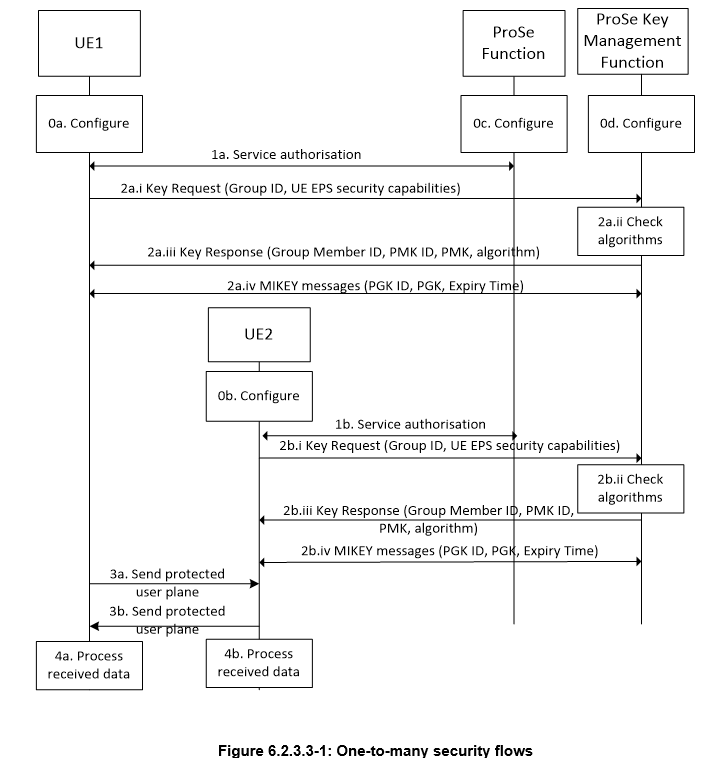
This is part of the key management procedures over PC8 interface as specified in TS 33.303 Sub-clause 6.2.3 The following Diagram is from TS 33.303.
There are two types of messages. One is Key Request and Response messages carried on HTTPS. The other is MIKEY messages used to transmit the keys. The port number on PKMF for MIKEY is 2269. Key Request/Response Transaction (3GPP TS 33.303 [34])As specified in TS 33.303 Annex E1, E2, E3, and E4, Key Request and Key Response messages between UE and ProSe KMF are based on HTTP 1.1, and the messages are contained in the HTTP message body as XML format. Landslide has provided Key Management Action in the HTTP script to perform this procedure. There will be one HTTP POST message from UE to PKMF and one HTTP 200 OK message from PKMF to UE. Key RequestWhen sending a Key Request message to request the ProSe Key Management Function to send PGKs or to change the groups for which it wants to receive keys, the UE shall include the following information:
The ProSe Key Management Function shall check that the UE is authorised to receive keys for the requested groups. This is done by using the UE identity that is bound to the keys that established the TLS tunnel in which the message is sent. It also checks that the UE supports the confidentiality algorithm required for each group. If the UE doesn’t then the ProSe Key Management Function responds with the appropriate error for that group. The ProSe Key Management Function shall update the stored set of the groups for which the UE will be sent keys. Key Request XML
Key ResponseThe ProSe Key Management Function responds to the UE with a Key Response message that includes the following parameters:
For the groups that the UE will get keys for, the UE shall store the received information associated with that group identity. If a PMK and PMK identity are included, the UE shall store these and delete any previously stored ones for this ProSe Key Management Function. Key Response XML
MIKEY Messages (3GPP TS 33.303 [35])
MIKEY is used to transport the PGKs from the ProSe Key Management Function to the UE. MIKEY is used with pre-shared keys as described in RFC 3830 [13]. The PMK (1.1.2) shared by the ProSe Key Management Function and the UE will be used as the pre-shared secret. The UDP port for MIKEY is 2269. ProSe Key Management Function may use the initial MIKEY message (by setting the PGK_ ID to all zeros) to trigger a Key Request message from the UE. Initial MIKEY Message (ProSe Key Management Function → UE)Initial MIKEY Payload:
Process Initial MIKEY Message (UE)When receiving the MIKEY message from ProSe Key Management Function, UE will process:
MIKEY Verification Message (UE → ProSe Key Management Function)
|
||
|
ProSe Downloading/Updating PSDK (success, no auth) |
Select ProSe Downloading/Updating PSDK (success, no auth).
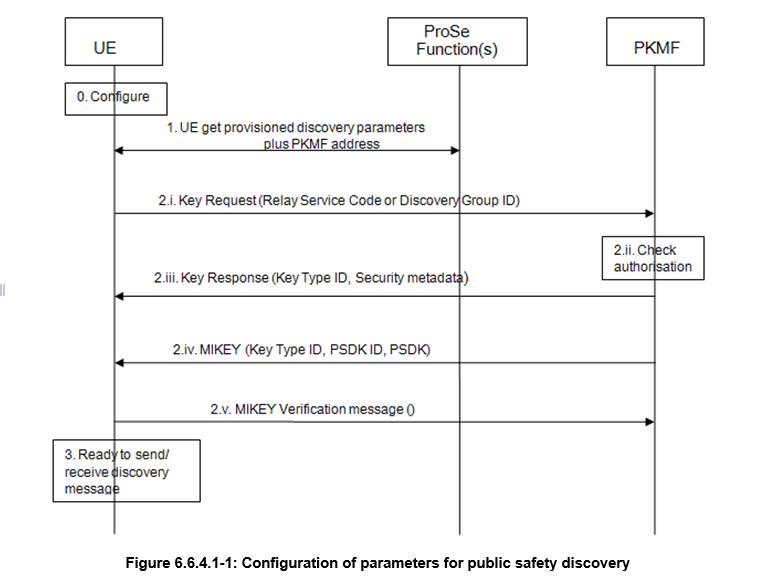
Downloading/Updating PSDK - This is part of the key management procedures over PC8 interface as specified in TS 33.303 Sub-clause 6.6.3. The following diagram is from TS 33.303.
Key Request/Response Transaction - See above section for PGKKey RequestKey Request XML
2.1.2. Key ResponseKey Response XML
MIKEY MessagesSame as PGK Section listed above, except for :
|
||
|
ProSE MIKEY Transaction |
Select for ProSE MIKEY Transaction.
See MIKEY Message Payload below. |
||
|
Wait For Time |
Halt a script for a specified amount of time.
|
XML Key Parameters
1. Transaction ID (<transaction-ID>)This parameter is used to uniquely identify a ProSe Key management transaction. The UE shall set this parameter to a new number for each outgoing new discovery request. The transaction ID is an integer in the 0-255 range. 2. Supported Algorithm (<AlgorithmAvailable>).This parameter is used to indicate which encryption algorithm the UE supports for one-to-many communications. It is a 1 octet long binary parameter encoded as shown: EPS encryption algorithms supported (octet 1)
3. Group ID (<GroupID>)This parameter is used to indicate the Group that the UE is requesting keys for. It is an integer in the 0-167777215 range. 4. PGK ID (<PGKId>)This parameter is used to indicate the PGK IDs for a particular group. It is an integer in the 0-255 range. 5. Error Code (<Error-Code>)This parameter is used to indicate the particular reason why the UE will not be receiving keys for a requested group. It is an integer in the 0-255 range encoded as follows:
6. Group Member ID (<GroupMemberID>This parameter is used as the identity of the UE within a Group. It is an integer in the 0-167777215 range. 7. Algorithm Info (<AlgorithmInfo>)The purpose of the Algorithm info is to indicate the confidentiality algorithms to be used for ciphering protection of the particular group traffic. It is a binary parameter of length 1 octet that is encoded as shown in table E.5.2.2.7-1. Type of ciphering algorithm (octet 1, bit 5 to 7) 8. PMK ID (<PMK-ID>)This parameter is used to identify a PMK. It is an 8 octet long binary parameter. 9. PMK (<PMK>)This parameter is a key that is used to protect MIKEY messages. It is a 32 octet long binary parameter. 10. Discovery Group ID (<DiscoveryGroupID>)This parameter is used to indicate the Discovery Group ID for which the UE is requesting keys. It is a 24-bit long string. 11. Relay Service Code (<RelayServiceCode>)This parameter is used to indicate the Relay Service Code for which the UE is requesting keys. It is a 24-bit long string. 12. PSDK ID (<PSDKId>)This parameter is used to indicate the PSDK IDs for a particular Relay Service Code or Discovery Group ID. It is an integer in the 0-255 range. 13. PGKA 256-bit binary number. 14. PSDKA 256-bit binary number.
|
MIKEY Message Payload
Payload Encoding1.1. Overall
0 1 2 3 4 5 6 7 8 9 0 1 2 3 4 5 6 7 8 9 0 1 2 3 4 5 6 7 8 9 0 1
+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+
! version ! data type ! next payload ! ! +-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+... + ~ Common Header... ~ ! ! +-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+
! next payload ! Payload 1 ... ! +-+-+-+-+-+-+-+-+ + ~ ~ +-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+
: : : : : : +-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+
! next payload ! Payload x ... ! +-+-+-+-+-+-+-+-+ + ~ ~ +-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+
! MAC/Signature ~ +-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+
MIKEY payload message example. Note that the payloads are byte aligned and not 32-bit aligned.
1.2. Common Header Payload (HDR)1 2 3 0 1 2 3 4 5 6 7 8 9 0 1 2 3 4 5 6 7 8 9 0 1 2 3 4 5 6 7 8 9 0 1
+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+
! version ! data type ! next payload !V! PRF func ! +-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+
! CSB ID ! +-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+
! #CS ! CS ID map type! CS ID map info ~ +-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+
* version (8 bits): the version number of MIKEY. version = 0x01 refers to MIKEY as defined in this document.
* data type (8 bits): describes the type of message (e.g., public- key transport message, verification message, error message)
Data type | Value | Comment --------------------------------------
Pre-shared | 0 | Initiator's pre-shared key message PSK ver msg | 1 | Verification message of a Pre-shared | | key message Public key | 2 | Initiator's public-key transport message PK ver msg | 3 | Verification message of a public-key | | message D-H init | 4 | Initiator's DH exchange message D-H resp | 5 | Responder's DH exchange message Error | 6 | Error message Table 6.1.a * next payload (8 bits): identifies the payload that is added after this payload.
Next payload | Value | Section ------------------------------
Last payload | 0 | - KEMAC | 1 | 6.2 PKE | 2 | 6.3 DH | 3 | 6.4 SIGN | 4 | 6.5 T | 5 | 6.6 ID | 6 | 6.7 CERT | 7 | 6.7 CHASH | 8 | 6.8 V | 9 | 6.9 SP | 10 | 6.10 RAND | 11 | 6.11 ERR | 12 | 6.12 Key data | 20 | 6.13 General Ext. | 21 | 6.15 Table 6.1.b
Note that some of the payloads cannot directly follow the header
(such as "Last payload", "Signature"). However, the Next payload field is generic for all payloads. Therefore, a value is allocated for each payload. The Next payload field is set to zero (Last payload) if the current payload is the last payload.
* V (1 bit): flag to indicate whether a verification message is expected or not (this only has meaning when it is set by the
Initiator). The V flag SHALL be ignored by the receiver in the DH method (as the response is MANDATORY).
V = 0 ==> no response expected V = 1 ==> response expected * PRF func (7 bits): indicates the PRF function that has been/will be used for key derivation.
PRF func | Value | Comments --------------------------------------------------------
MIKEY-1 | 0 | Mandatory (see Section 4.1.2) Table 6.1.c
* CSB ID (32 bits): identifies the CSB. It is RECOMMENDED that the CSB ID be chosen at random by the Initiator. This ID MUST be unique between each Initiator-Responder pair, i.e., not globally
unique. An Initiator MUST check for collisions when choosing the ID (if the Initiator already has one or more established CSBs with
the Responder). The Responder uses the same CSB ID in the response.
* #CS (8 bits): indicates the number of Crypto Sessions that will be handled within the CBS. Note that even though it is possible to use 255 CSs, it is not likely that a CSB will include this many
CSs. The integer 0 is interpreted as no CS included. This may be the case in an initial setup message.
* CS ID map type (8 bits): specifies the method of uniquely mapping Crypto Sessions to the security protocol sessions.
CS ID map type | Value
-----------------------
SRTP-ID | 0 Table 6.1.d
* CS ID map info (16 bits): identifies the crypto session(s) for which the SA should be created. The currently defined map type is the SRTP-ID (defined in Section 6.1.1). 1.3. Timestamp Payload (T)The timestamp payload carries the timestamp information. 1 2 3 0 1 2 3 4 5 6 7 8 9 0 1 2 3 4 5 6 7 8 9 0 1 2 3 4 5 6 7 8 9 0 1
+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+
! Next Payload ! TS type ! TS value ~ +-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+
* Next payload (8 bits): identifies the payload that is added after this payload. See Section 6.1 for values. * TS type (8 bits): specifies the timestamp type used. TS type | Value | Comments | length of TS value -------------------------------------|-------------------
NTP-UTC | 0 | Mandatory | 64-bits NTP | 1 | Mandatory | 64-bits COUNTER | 2 | Optional | 32-bits Table 6.6
Note: COUNTER SHALL be padded (with leading zeros) to a 64-bit
value when used as input for the default PRF.
* TS-value (variable length): The timestamp value of the specified TS type
1.4. RANDThe RAND payload consists of a (pseudo-)random bit-string. The RAND MUST be independently generated per CSB (note that if the CSB has
several members, the Initiator MUST use the same RAND for all the
members). For randomness recommendations for security, see [RAND]. 1 2 3 0 1 2 3 4 5 6 7 8 9 0 1 2 3 4 5 6 7 8 9 0 1 2 3 4 5 6 7 8 9 0 1
+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+
! Next payload ! RAND len ! RAND ~ +-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+
* Next payload (8 bits): identifies the payload that is added after this payload. See Section 6.1 for values. * RAND len (8 bits): length of the RAND (in bytes). It SHOULD be at least 16.
* RAND (variable length): a (pseudo-)randomly chosen bit-string. 1.5. IDi /IDrNote that the ID payload and the Certificate payload are two completely different payloads (having different payload identifiers).
However, as they share the same payload structure, they are described
in the same section.
The ID payload carries a uniquely defined identifier.
The certificate payload contains an indicator of the certificate
provided as well as the certificate data. If a certificate chain is to be provided, each certificate in the chain should be included in a
separate CERT payload.
1 2 3 0 1 2 3 4 5 6 7 8 9 0 1 2 3 4 5 6 7 8 9 0 1 2 3 4 5 6 7 8 9 0 1
+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+
! Next Payload ! ID/Cert Type ! ID/Cert len ! +-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+
! ID/Certificate Data ~ +-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+
* Next payload (8 bits): identifies the payload that is added after this payload. See Section 6.1 for values. If the payload is an ID payload, the following values apply for the
ID type field:
* ID Type (8 bits): specifies the identifier type used. ID Type | Value | Comments ----------------------------------------------
NAI | 0 | Mandatory (see [NAI]) URI | 1 | Mandatory (see [URI]) Table 6.7.a
If the payload is a Certificate payload, the following values applies
for the Cert type field:
* Cert Type (8 bits): specifies the certificate type used. Cert Type | Value | Comments ----------------------------------------------
X.509v3 | 0 | Mandatory X.509v3 URL | 1 | plain ASCII URL to the location of the Cert X.509v3 Sign | 2 | Mandatory (used for signatures only) X.509v3 Encr | 3 | Mandatory (used for encryption only) Table 6.7.b
* ID/Cert len (16 bits): the length of the ID or Certificate field (in bytes).
* ID/Certificate (variable length): The ID or Certificate data. The X.509 [X.509] certificates are included as a bytes string using DER encoding as specified in X.509.
1.6. KEYMACThe Key data transport payload contains encrypted Key data sub- payloads (see Section 6.13 for the definition of the Key data sub- payload). It may contain one or more Key data payloads, each including, for example, a TGK. The last Key data payload has its Next payload field set to Last payload. For an update message (see also Section 4.5), it is allowed to skip the Key data sub-payloads (which will result in the Encr data len being equal to 0).
Note that the MAC coverage depends on the method used, i.e., pre-
shared vs public key, see below.
If the transport method used is the pre-shared key method, this Key
data transport payload is the last payload in the message (note that
the Next payload field is set to Last payload). The MAC is then calculated over the entire MIKEY message following the directives in
Section 5.2. If the transport method used is the public-key method, the
Initiator's identity is added in the encrypted data. This is done by adding the ID payload as the first payload, which is then followed by
the Key data sub-payloads. Note that for an update message, the ID is still sent encrypted to the Responder (this is to avoid certain
re-direction attacks) even though no Key data sub-payload is added
after.
In the public-key case, the coverage of the MAC field is over the Key
data transport payload only, instead of the complete MIKEY message,
as in the pre-shared case. The MAC is therefore calculated over the Key data transport payload, except for the MAC field and where the
Next payload field has been set to zero (see also Section 5.2). 1 2 3 0 1 2 3 4 5 6 7 8 9 0 1 2 3 4 5 6 7 8 9 0 1 2 3 4 5 6 7 8 9 0 1
+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+
! Next payload ! Encr alg ! Encr data len ! +-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+
! Encr data ~ +-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+
! Mac alg ! MAC ~ +-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+
* Next payload (8 bits): identifies the payload that is added after this payload. See Section 6.1 for defined values. * Encr alg (8 bits): the encryption algorithm used to encrypt the Encr data field.
Encr alg | Value | Comment -------------------------------------------
NULL | 0 | Very restricted usage, see Section 4.2.3! AES-CM-128 | 1 | Mandatory; AES-CM using a 128-bit key, see Section 4.2.3) AES-KW-128 | 2 | AES Key Wrap using a 128-bit key, see Section 4.2.3 Table 6.2.a
* Encr data len (16 bits): length of Encr data (in bytes). * Encr data (variable length): the encrypted key sub-payloads (see Section 6.13). * MAC alg (8 bits): specifies the authentication algorithm used. MAC alg | Value | Comments | Length (bits) ----------------------------------------------------------
NULL | 0 | restricted usage | 0 | | Section 4.2.4 | HMAC-SHA-1-160 | 1 | Mandatory, | 160 | | Section 4.2.4 | Table 6.2.b
* MAC (variable length): the message authentication code of the entire message.
1.7. Verification Message Payload (V) The Ver msg payload contains the calculated verification message in
the pre-shared key and the public-key transport methods. Note that the MAC is calculated over the entire MIKEY message, as well as the
IDs and Timestamp (see also Section 5.2). 1 2 3 0 1 2 3 4 5 6 7 8 9 0 1 2 3 4 5 6 7 8 9 0 1 2 3 4 5 6 7 8 9 0 1
+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+
! Next Payload ! Auth alg ! Ver data ~ +-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+
* Next payload (8 bits): identifies the payload that is added after this payload. See Section 6.1 for values. * Auth alg (8 bits): specifies the MAC algorithm used for the verification message. See Section 6.2 for defined values. * Ver data (variable length): the verification message data. The length is implicit from the authentication algorithm used
|